The Control Panel enables you to configure protection settings for your subscribed security modules and add-ons. The Control Panel is also where you administer your workspace, cloud applications, protected users, and their devices.
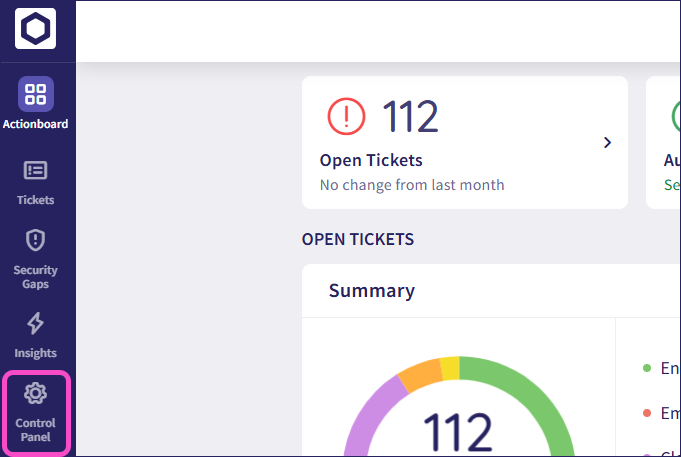
To access the Control Panel, sign in to the Coro console and from the sidebar, select Control Panel:
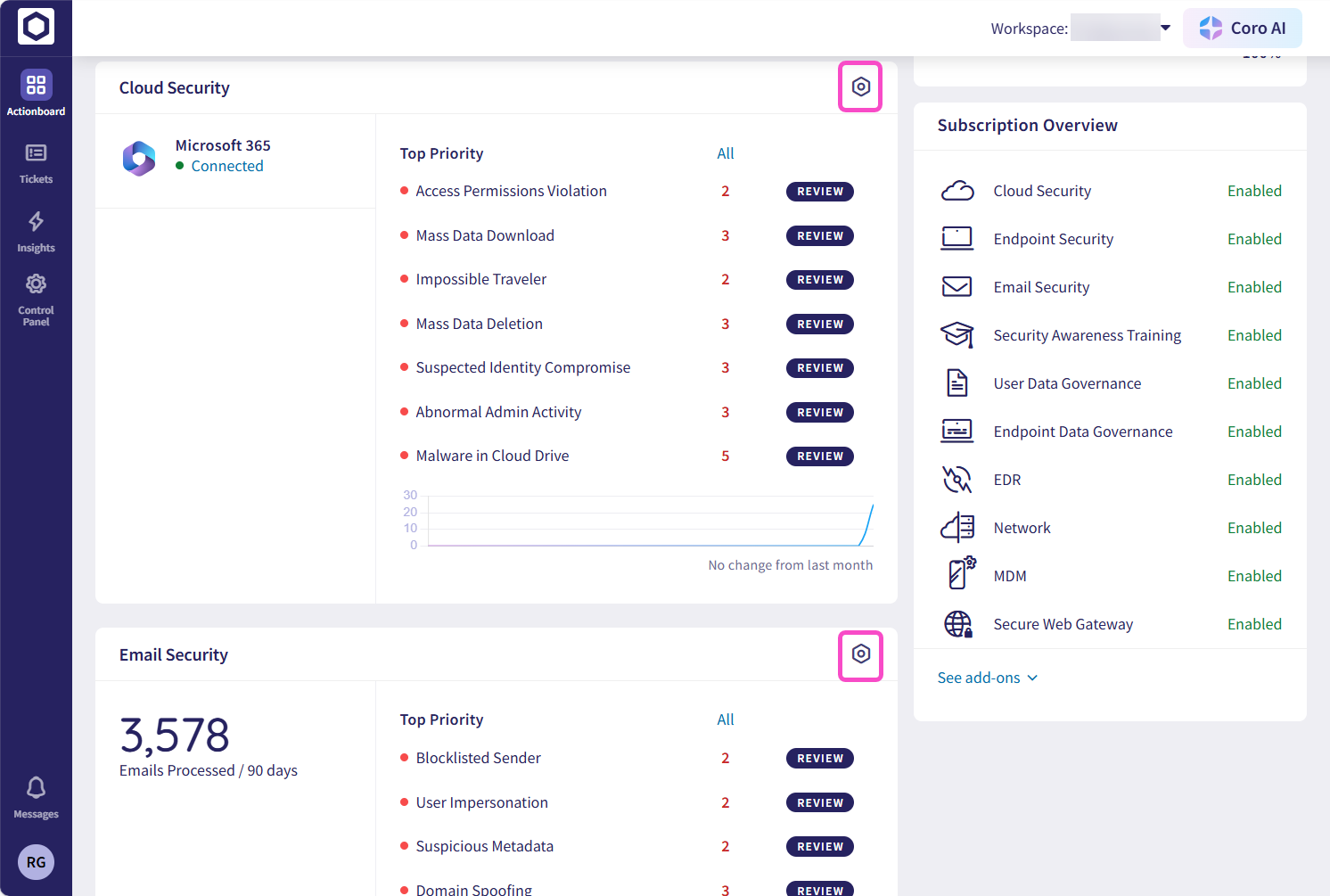
In addition, each dashboard panel (and optional module or add-on) in the Actionboard includes a Control panel icon, designed to enable you to quickly access the relevant settings page:
The Control Panel contains the following options, separated into Protection and Workspace:
Coro displays modules that aren't part of your subscription as disabled.
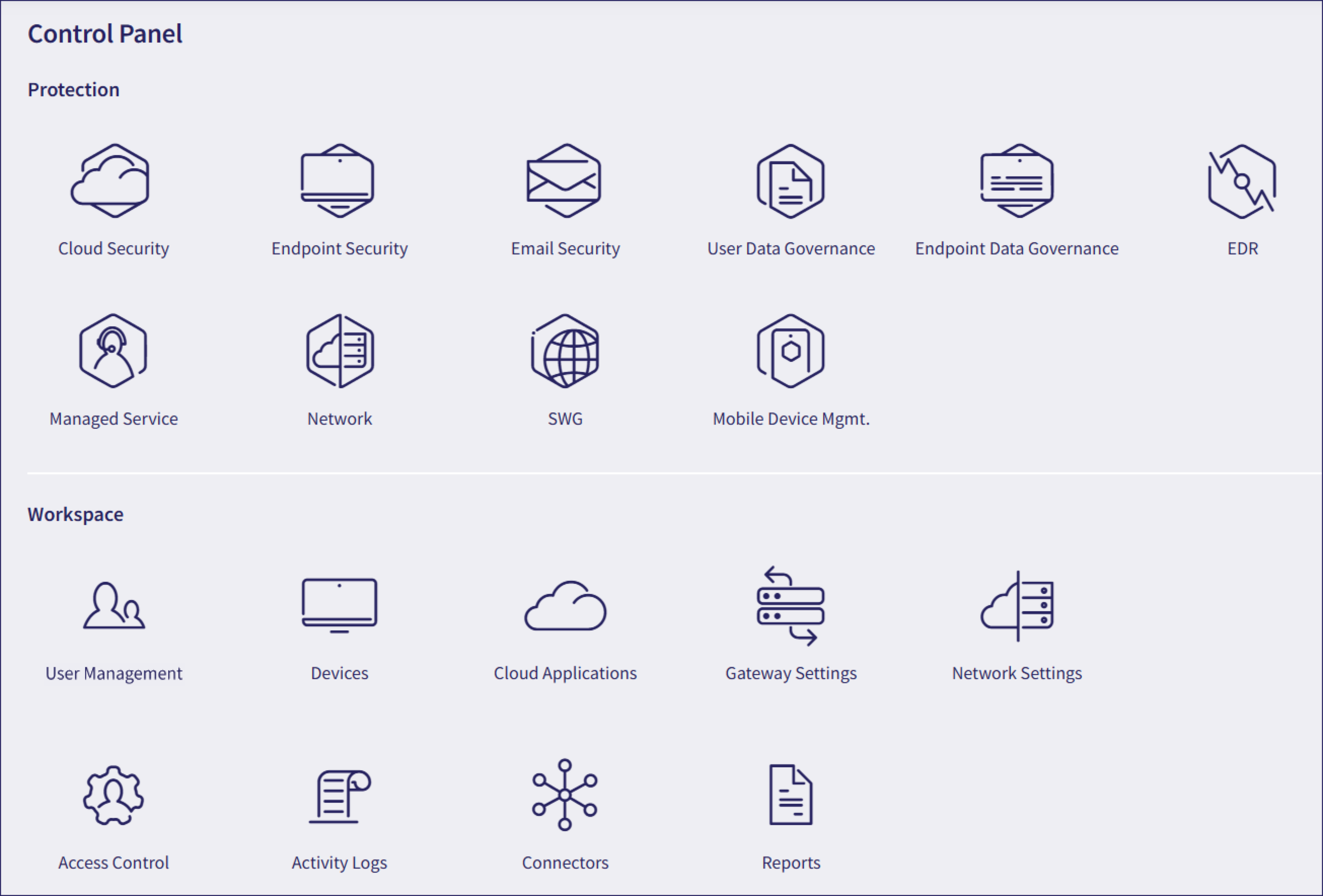
Select an object to access the settings page for that component.
At the bottom of the page, Coro displays your workspace name and workspace ID.

Monitor and control access to connected cloud applications and data. See Setting permissions for your cloud applications.
Manage the protection features for endpoint devices. See Introducing Coro Endpoint Security.
Configure email security settings, including trusted and untrusted domain lists. See Introducing Email Security.
Manage your users' access to sensitive information and configure how Coro monitors data sharing. See Introducing User Data Governance.
Configure monitoring for storage of sensitive information on your users' endpoint devices. See Introducing Endpoint Data Governance.
Access the Endpoint Detection and Response module page. See Coro Endpoint Detection and Response (EDR).
Access the Managed Service page. See Managed Service.
Access the Network module page. See Network.
Access the Secure Web Gateway (SWG) page. See SWG.
Access the Security Awareness Training module page. See Security Awareness Training.
Access the Mobile Device Management module page. See Mobile Device Management with Coro.
Manage lists of your users and user groups. See Adding users and user groups for protection.
Get Coro Agent deployment packages, manage device labels, and configure monitoring settings. See Introducing devices.
Connect cloud applications to be monitored for users. See Introducing cloud security.
Configure inbound and outbound gateways to monitor and protect your incoming and outgoing email. See Introducing the Inbound Gateway or Configuring an outbound gateway for email scanning.
Configure settings for your Network service, which apply to the Network and SWG modules. See Network Settings.
Manage admin users, add new admin users, set roles and permissions, and review active sessions. See Introducing Access Control.
View the activity logs for your workspace. See Activity Log.
Configure connectors for integrating Coro with external Security Information and Event Management (SIEM) services. See Security Information and Event Management (SIEM) integration.
View, download, and export activity summary reports for your workspace. See Viewing reports.