Coro's Endpoint Security module is your first line of defense against endpoint threats such as malware and ransomware.
By installing Coro's Agent application on your organization's endpoint devices, Endpoint Security can monitor and protect against common threats and suspicious activity. Through the Agent, Coro can often automatically remediate security incidents without admin intervention.
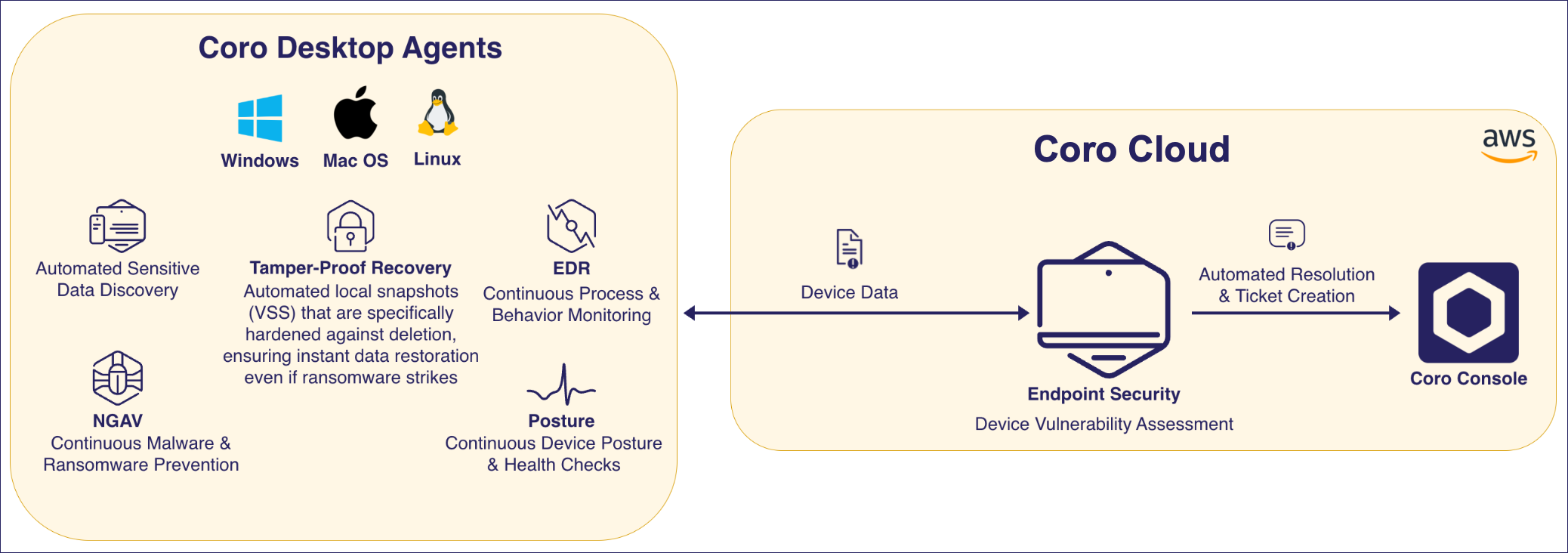
Coro uses a unique threat intelligence model to identify malicious activity and anomalous behavior inconsistent with normal usage. Endpoints also benefit from enhanced backup and recovery defense, where device snapshots are hardened against tampering and deletion (a common activity of ransomware).
Coro can additionally help protect devices through enforcement of a strong security posture - by ensuring devices are up to date and properly configured with the correct defenses in place.
Read the articles in this chapter to learn about how Coro Endpoint Security can protect your devices through:
- Setting device posture policies. See Device posture configuration overview.
- Configuring NGAV device monitoring settings. See Next Generation Anti Virus (NGAV) settings.
- Managing files and folders that Coro allows or blocks. See Endpoint Security allowlist and blocklist.
- Scheduling regular malware scans. See Scheduled malware scans.
- Detecting wireless network phishing. See Wi-Fi Phishing.
Coro extends device security through the Endpoint Detection and Response module, providing deep monitoring and analysis of malicious activity in device files and processes. To learn more, see Coro Endpoint Detection and Response (EDR).
Coro also offers Mobile Device Management, a module to manage iOS/iPadOS and Android mobile devices for end users across your organization. To learn more, see Mobile Device Management with Coro.
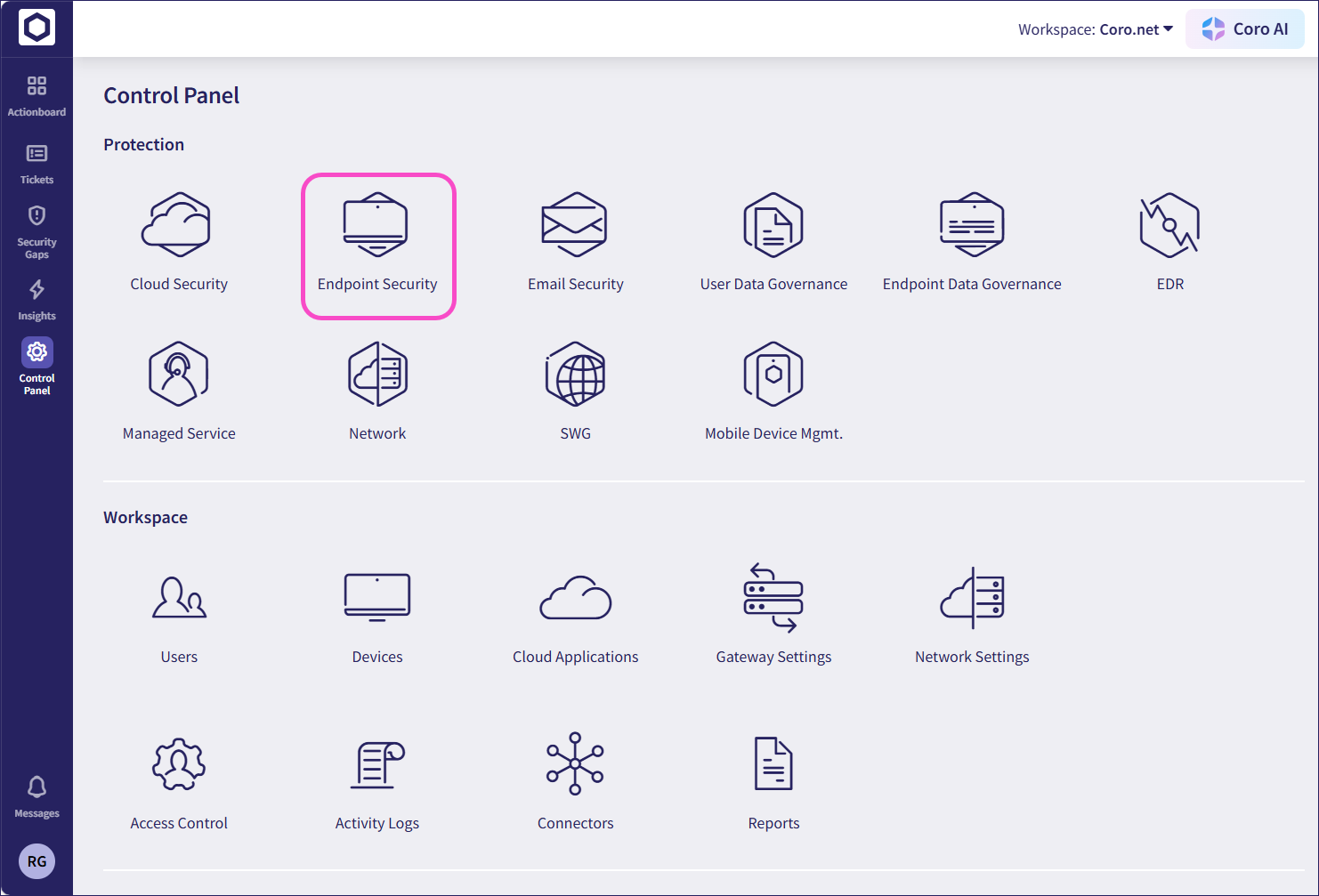
To access the Endpoint Security module:
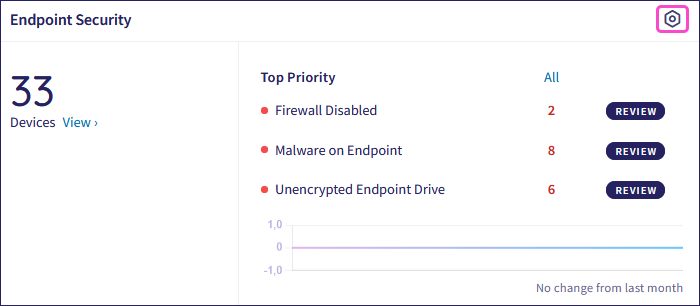
From the Actionboard, select Control Panel from the top of the Endpoint Security dashboard panel:
Alternatively, from the sidebar, select Control Panel > Endpoint Security: