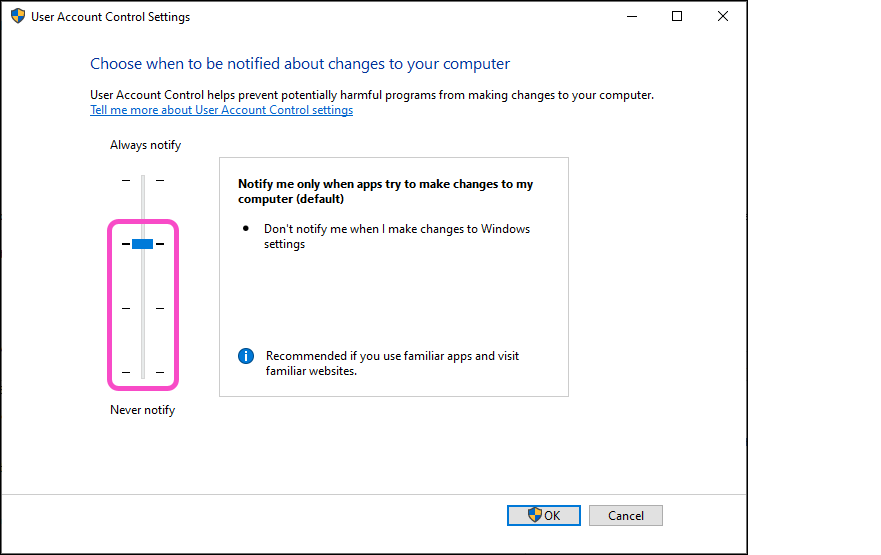
Coro enforces the UAC Notification Missing policy when Windows User Account Control settings are set to:
Default
Low
Medium
For more information, see UAC Notification.
The Coro agent is capable of extracting user profile information directly from your device to determine the age of your existing password.
For more information, see Remote password and session locking.
While Coro can perform hard drive encryption, there is no method to ensure this functionality is auto-enforced. It is a manual remediation action performed by an admin user in the Coro console, either from the Devices page or from the Ticket Log.
For more information, see Encrypting endpoint device drives
Coro maintains a record of the previous three signed-in users.
No, if a potentially malicious file has already been quarantined by another AV product, Coro does not detect it.
Coro advises against running another AV product in addition to Coro. For more details, see Running other antivirus software with Coro.
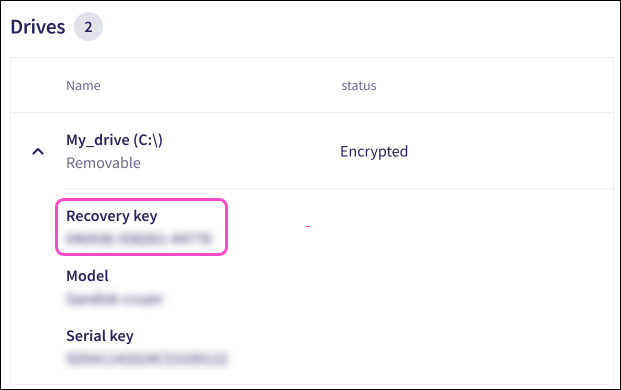
Encryption keys are stored on both the device (by BitLocker) and on the Coro servers.
Additionally, BitLocker recovery keys are displayed for all encrypted drives on a device. The recovery key is displayed within the expanded Drives section of the affected device on the Devices and Global devices pages:
For more information, see Encrypting endpoint device drives
Yes, an admin user with sufficient permissions can disable protection for a device in the Coro console and then remove the device from Coro monitoring.
To disable protection on endpoint devices as an admin user:
Access the Devices page.
Locate and select the required device, then select Actions > Disable protection.
After the set heartbeat interval elapses, Coro disables protection on the devices, allowing the user to uninstall Coro.
No, Coro does not detect data governance issues within CAD files.
No. Coro does not remediate tickets retroactively. Coro monitors, generates, and remediates tickets only while the workspace is active. If the workspace becomes inactive before remediation occurs, Coro does not take action on existing tickets, even if the workspace is later reactivated through a trial extension or subscription purchase.
Running other AV software alongside Coro is discouraged because it can cause performance conflicts.
For more information, see Running other antivirus software with Coro.
Coro monitors all processes and terminates them if suspicious behavior is detected.
When Advanced Threat Control is enabled, Coro monitors active processes for known and potential threats, and blocks processes (that are not explicitly allowlisted) that exhibit suspicious behavior.
The Endpoint Security and EDR module Allow/Block lists allow you to manage your processes by allowing those that are safe to be accessed.
For more information, see:
Yes. For more information, see Deploying Coro on Linux devices.
No.
Yes.
The entire hard drive of the device. Windows uses the Volume Shadow Copy Service (VSS) to perform the backup.
For further information, see Secured shadow backups.
Windows uses the Volume Shadow Copy Service (VSS) to store secure shadow backup snapshots in the hidden System Volume Information folder. You can manage these backups through the device’s system protection settings.
For further information, see Using VSS backup protection on your Windows endpoints.
For instructions on how to restore secure shadow backup snapshots, see Restoring secure shadow backup snapshots.
The USB Lockdown device posture policy blocks mass storage devices on macOS devices. For Windows devices, this extends to block both mass storage and other USB-connected devices, such as media players and smartphones.
Admin users can allow specific USB devices by their serial number when configuring a USB Lockdown device policy.
For more information, see Endpoint device USB Lockdown.
Your device has a Wi-Fi connection policy enabled. Wi-Fi connection policies prevent devices from connecting to public Wi-Fi networks, only allowing connections to secure, password protected networks.
Admin users can allow the connection by ensuring no device labels that enforce this Wi-Fi connection policy are assigned to your device. Alternatively, they can remove the Wi-Fi connection policy from all devices.
Your device must first connect to a secure network to update its policy. After the policy update, your device is able to connect to public Wi-Fi networks.
The time taken for the Wi-Fi connection policy to update depends on your workspace's heartbeat interval.
For more information, see Configuring Wi-Fi connectivity policies.
The Approve This File and Exclude Folder from Malware Scan actions extend to all devices within the workspace.
If you set password policies via Active Directory, then you do not need to configure password policies in Coro. Active Directory password policies override Coro password policies.
Coro shows information regarding the status of the most recent endpoint device malware and sensitive data scans on the Devices page. Additionally, if a scan detects malware or ransomware on a device, corresponding tickets are created and are viewable in the ticket log.
For further information about tickets, see Ticket types for Endpoint Security.
Coro groups related processes into process groups (collections of processes that share a common origin or behavior) when it generates infected process tickets. If Coro creates an Infected process ticket, you can select Approve process group from the ticket actions menu. When an admin user with sufficient permission approves the process group, the Coro Agent applies the approval across all devices in the same workspace. Coro also considers identical process groups safe and no longer terminates them.
If Coro creates a Malware on endpoint ticket, you can either select Approve this file or Exclude folder from malware scan from the ticket actions menu:
Approve this file: The Agent removes the file from quarantine (if applicable) and applies the approval to all devices in the workspace. Identical files are not quarantined in the future.
Exclude folder from malware scan: Coro skips the specified folder in future malware and ransomware scans.
For further information, see Ticket types for Endpoint Security.
No, Coro's AV does not have a ransomware rollback feature. However, admin users with sufficient permissions can enable Secured Shadow Backups on Windows devices. When enabled, Coro enforces backup snapshots every four hours and blocks processes that exhibit risks to the backup. The Coro Agent utilizes the Windows Volume Shadow Copy Service (VSS) mechanism to automatically save a snapshot of your device's files.
Yes, Coro automatically retrieves and stores device encryption recovery keys, even if Coro did not initiate the encryption.
Coro supports this functionality for Windows devices only.
No, mobile devices can still charge while a USB lockdown device posture policy is active on the device. A USB lockdown device posture policy can block:
Portable devices: (Windows devices) USB-connected mobile devices.
Mass storage devices: (Windows and macOS devices) USB flash drives and external hard drives.
For more information, see USB Lockdown.
Yes, Coro encrypts the entire disk drive by default. BitLocker encryption through Coro is applied per drive. The primary system drive must be encrypted first. If your device has multiple drives, you have the option to encrypt each one individually.
For more information, see Encrypting endpoint device drives.
If a device is offline during a scheduled scan, the scan automatically starts when the device reconnects to Coro.
For more information, see Scheduling a sensitive data scan.
Coro enforces Remote Password & Session Locking policies.
Coro immediately implements screen lockout policies and applies password policies when:
- The user logs off the device.
- The device restarts.
- The device enters screen lock.
Lockout duration: Specifies how long a user's screen remains locked after the lockout is activated (maximum value 3 hours.)
Lockout threshold: (attempts): Specifies the number of consecutive failed login attempts that triggers a screen lockout (maximum value 10).
You must set both parameters to configure a screen lockout policy.
For further information, see Remote password and session locking.
Coro is designed to provide real-time antivirus scanning for continuous protection of your endpoint devices. Consequently, Coro does not provide the ability to selectively schedule antivirus scans. The Coro Agent operates in real-time, scanning files whenever a user or process attempts to access them. If a file is identified as malicious, Coro quarantines it. Coro also detects and terminates potentially malicious processes.
Advanced threat control (ATC) provides an additional layer of real-time monitoring by analyzing processes as they run/execute for known and potential threats. ATC blocks any processes that exhibit suspicious behavior.
No, the USB Lockdown policy only blocks:
Portable devices: (Windows devices) USB-connected mobile devices.
Mass storage devices: (Windows and macOS devices) USB flash drives and external hard drives.
For further information, see Endpoint device USB Lockdown.
When Coro quarantines a malicious file on a device, it moves the file to the following location:
- Windows:
C:\ProgramData\CoroAgent1SRV\p\BD\quar - macOS:
/Library/Coro/RunShield/BD/quar
Yes.
Workspaces can be created with, or without, a maximum protected device limit. This is set as a part of a subscription agreement. For more information, see Protection limits.
Yes, select Open remote shell from any online device listed on the Devices or Global devices page. This action starts a command prompt on the device, allowing you to run commands remotely.
For more information, see Device actions.
The Disable protection action deactivates Coro protection on a device. To re-enable Coro protection, go to the Activity Log, find the related entry, and select UNDO.
After your password expires, the operating system typically displays a prompt for the user to update it during their next sign in.
The Wi-Fi Connection policy blocks access to public wireless networks for specific devices or groups. The Wi-Fi Phishing add-on integrates with the Endpoint Security module to detect potentially malicious wireless network connections, such as those used in Man-in-the-Middle attacks that can steal or manipulate data.
Coro considers a network encrypted if it uses WPA or a higher standard.
Coro applies policies to all supported devices linked to a label, regardless of operating system. Features activate only on devices that support them.
Yes.
No. Coro uses built-in tools (BitLocker on Windows and FileVault on macOS) to enforce encryption on a device’s drives. This protects data in case the device is lost or stolen, but does not make the device unusable.
Yes. For more information, see Endpoint Security allowlist and blocklist.
When you delete an unencrypted endpoint drive policy for a specific group of devices (specified by a device label), Coro no longer creates tickets for unencrypted endpoint drives assigned to that device label.
While Coro does not support wildcard characters, the Windows and macOS Agents support environment variables. Use these variables in place of specific file or folder paths to simplify policy configuration and reduce the number of manual entries.
For more information, see Using environment variables.
No. Coro does not provide an option to disable BitLocker itself. You must disable it directly in Windows.
For more information, refer to Microsoft's BitLocker documentation (https://learn.microsoft.com/en-us/powershell/module/bitlocker/?view=windowsserver2025-ps).
Yes. Admin users can allow specific USB devices by their serial number when configuring a USB Lockdown device policy.
For more information, see USB Lockdown.
No. Coro does not automatically distinguish between company-owned and personal (BYOD) devices. However, admin users can view device names on the Devices page and manually disable protection on unauthorized devices. To maintain control, Coro recommends deploying the agent through a remote monitoring and management (RMM) tool. This approach enables admin users to control exactly which devices receive the Agent.
Device actions take effect after the device checks in at its next heartbeat interval.
No.
The Coro installation file includes a workspace-specific activation key. To move a device to a different workspace, you must uninstall Coro from the device and reinstall it using the installer from the correct workspace.
Yes. Coro detects a drive as encrypted even if only the used space is encrypted. However, Coro does not indicate whether the encryption is full or partial.
Enter each wireless network name as its SSID.
SSIDs are case-sensitive.
For more information, see Wi-Fi Connection.
Yes.
For more information, see Wi-Fi Phishing.
Yes, Coro shows real-time scan progress in the Devices page. Coro also logs the scan initiation in the Activity Log and notifies the end user in the Agent app when the scan starts and completes.
Coro does not control VSS storage settings; Windows manages them. Coro recommends setting the threshold to 15–20% of the total drive capacity.
Coro automatically sets the threshold to 10% if it detects the value is below 9%.
No. When you start using a new device, Coro treats it as an additional device rather than a replacement. Coro does not automatically remove the old device from your workspace. To remove the old device, go to the Devices page, open the action menu for that device, and select Actions > Disable protection.
For more information, see:
Yes. When a user attempts to connect to a suspicious wireless network, Coro displays a notification on the device. Coro also creates a WiFi Phishing ticket for the admin user to review.
Coro monitors the Allow applications downloaded from setting on macOS devices. If this setting is set to Anywhere, Coro creates a Gatekeeper Disabled ticket.
When Coro isolates a device, it uses the device’s local firewall to block all inbound and outbound network communication. The only connection that remains active is to Coro’s servers, allowing Coro to continue managing the device and perform actions remotely.
Yes, Coro detects malicious files inside containers (archives such as ZIP, RAR, other compressed formats, or self-extracting installers like .exe files).
For more information, see Quarantine infected containers.
Yes, Coro supports encryption on macOS internal drives and external Apple File System drives.
No, Coro quarantines the infected file to prevent it from causing harm but does not delete it from the device.
Yes, Coro actively protects VSS backups by enforcing automatic snapshots every four hours and blocking processes that pose a risk to those backups.
Yes. When both policies are in place, Coro allows the device to connect to the specified open (unencrypted) wireless network. The allow rule takes precedence over the restriction on unencrypted wireless networks.
Coro supports platform-specific scan intervals. On Windows devices, you can schedule scans to run daily or every two days. On macOS and Linux devices, Coro supports a minimum interval of every three days.
If a device is offline at the scheduled time, Coro automatically starts the scan when the device next comes online.
Agent health filters are part of the Status section of the Groups filter on the Devices and Global devices pages. They enable admin users and MSP admin users to filter devices experiencing Agent-related issues, including required device restarts, conflicts with other antivirus products that may affect Coro's Agent performance, or devices running outdated Agent versions.
Additional devices can still be added, but they will be marked as Unlicensed and will not receive protection.
The device protection limit for a workspace is based on a ratio of three devices per protected user, managed as a total pool across the workspace rather than enforced per individual user. If a single user has only one device connected, the remaining two slots can be filled by other users.
The console displays a banner on the Devices page indicating that the limit has been exceeded. A related security gap is also generated.
After licenses are added to a subscription, unlicensed devices can be assigned a license and transition to a fully protected state.
Yes. Scheduled scans are added to the Activity Log when they start, ensuring full visibility and auditability of all scan activity.
Yes. The Activity Log captures the complete scan lifecycle, including start, stop, and completion events, along with timestamps, initiator, and results. Coro provides a link against completed scans in the Devices page to enable you to view relevant scan activity log entries.