Regulatory sensitive information
Sensitive data is information considered private or protected by law, policy, or contractual obligation. Coro detects sensitive data in user emails and cloud drives that might be subject to regulatory or compliance requirements, such as content shared from OneDrive, Google Drive, Box, or Dropbox.
note
Each organization is unique and is required to comply with specific sensitive data regulatory requirements. Use the Coro interactive discovery tool to assess your specific data governance needs.
The following table shows the data transactions monitored by Coro. It includes information on the type of monitoring (data access, data exposure, or both):
| Transaction | Monitoring |
|---|---|
| Content and attachments of internal (inbound and outbound) email between protected users | Access |
| Content and attachments of outbound email | Access and exposure |
| Content and attachments of inbound email | Access and exposure |
| Internal and external sharing of cloud drive files | Access and exposure |
Coro categorizes sensitive data objects it can monitor and expose into four types:
Important
For information on the sensitive data that Coro recognizes, see Sensitive data recognized by Coro.
Credit card data
Credit card data is data found on or associated with credit cards. Credit card data includes, but is not limited to:
- Card expiration dates
- Cardholder names
- Card numbers
- Card verification values (CVVs)
Health data
Health data is data collected, stored, used, or transmitted during the provision of health care services. Health data includes, but is not limited to:
- Health insurance information
- Medical history
- Name
Non-public data
Non-public data is personal financial data that is collected and stored by financial institutions. Non-public data is a combination of personal data and other sensitive data types. For example, social security numbers (SSNs) are personal data types, but in combination with credit card data, they are also classified as non-public data.
Coro generates either an open or closed Non-Public Data ticket based on the type and combination of detected sensitive data, as outlined below:
- Coro generates a closed Non-Public Data ticket when it detects personal data and another sensitive data type, such as financial keywords (financial metadata, content, forms, or credit card data).
- Coro generates an open Non-Public Data ticket when it detects credit card data in addition to personal data.
For more information, see Ticket types for User Data Governance.
Personal data
Personal data is any data connected to a specific individual that can be used to uncover that individual's identity. Personal data includes, but is not limited to:
- Email address
- Full name
- Social security numbers (SSNs)
Business sensitive data
Business or security data that is important to an individual organization. The following is considered business sensitive data:
- Certificates
- Critical data
- Passwords
- Sensitive file types
- Source code
Coro helps organizations in meeting security and privacy requirements set by several regulations. To comply, organizations may be required to implement regulatory policies or seek legal opinions from specialized firms while using Coro's services.
note
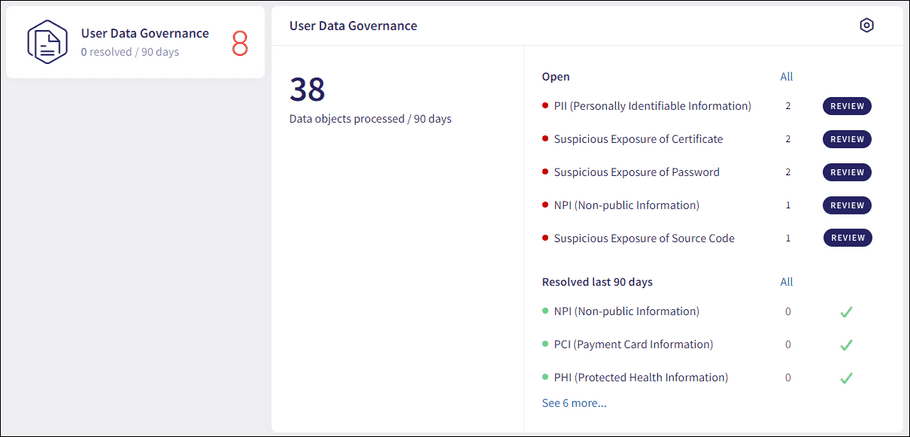
You can view tickets from the User Data Governance component on the Actionboard:
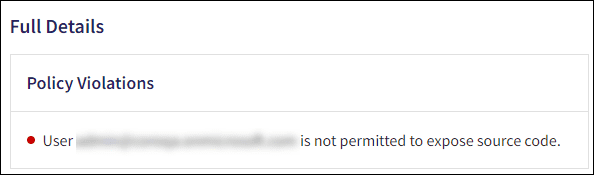
Policy violation
When a transaction violates a sensitive data policy, a policy violation occurs and a ticket is generated. The ticket displays the following details:
-
Policy violation
: The policy type that was violated, for example, unauthorized source code exposure: