Configuring a site-to-site VPN tunnel with Coro Network and Cisco Meraki¶
As part of a virtual office, Coro includes the ability for customers to configure VPNs together with site-to-site VPN tunnels.
This guide describes how to establish a site-to-site VPN tunnel between Coro and a Cisco Meraki appliance through the Cisco Meraki platform, and how to configure Coro to integrate with Cisco Meraki's firewall.
To configure a Cisco Meraki site-to-site VPN tunnel, complete the following processes:
Prerequisites¶
Before you start, make sure you have the following:
-
Access as an admin user to the Coro console for your workspace
-
An active subscription (or trial) for the Coro Network module
-
Access to the Cisco Meraki Dashboard
Configuring Cisco Meraki¶
Configure Cisco Meraki to allow traffic from inside and outside the network:
Important
The Cisco Meraki configuration method is the same whether Virtual MX (VMX) is hosted on Azure/AWS or is a physical device.
-
Sign into your Cisco Meraki Dashboard.
-
Select Network:
-
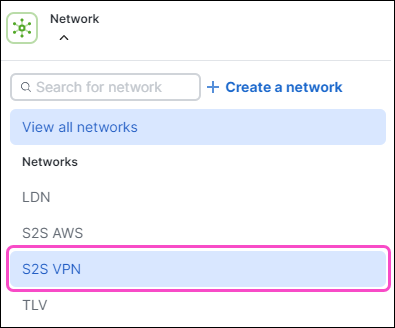
Select your preferred VMX appliance:
-
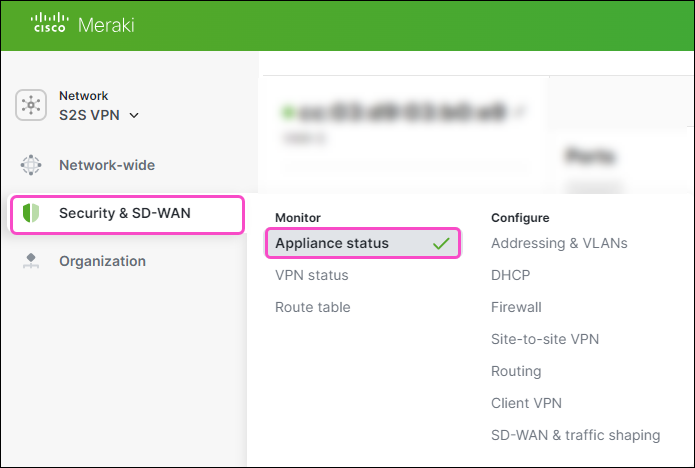
Go to Security & SD-WAN > Appliance status:
-
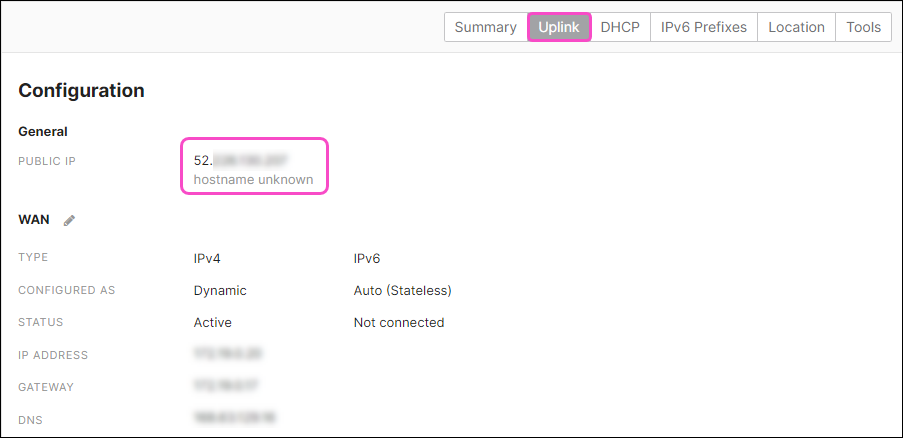
Select Uplink and note the PUBLIC IP address value:
-
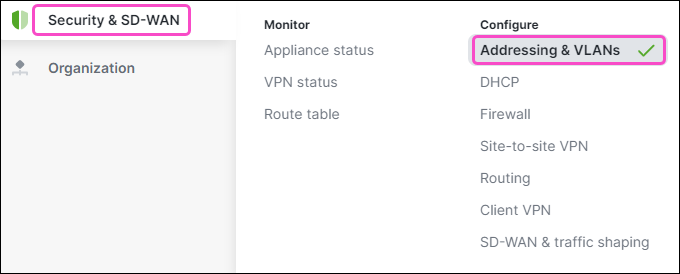
Go to Security & SD-WAN > Addressing and VLANs:
-
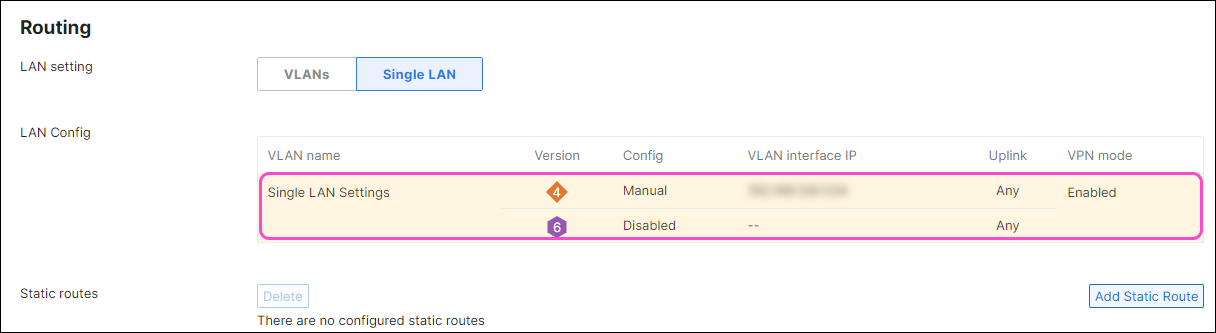
Under Routing, select the LAN Config table:
The Configure Single LAN dialog appears:
-
Note the Subnet value:
-
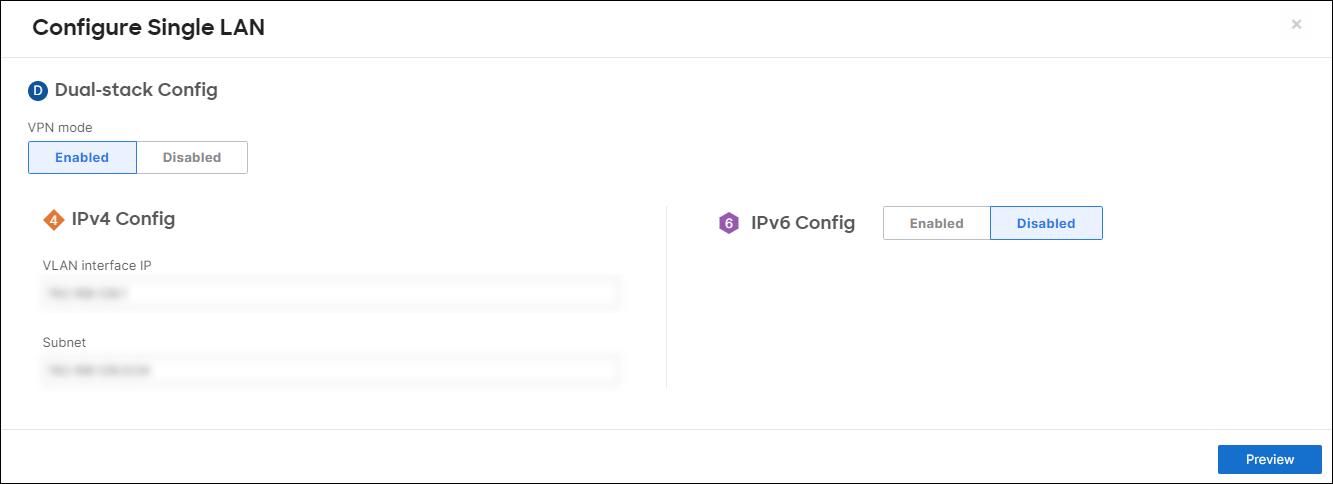
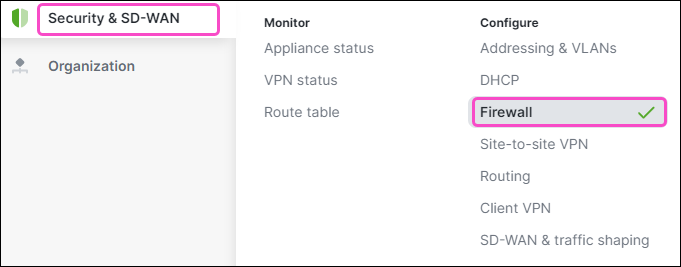
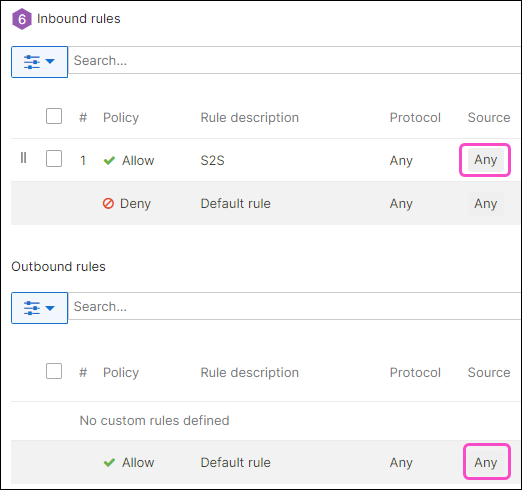
Go to Security & SD-WAN > Firewall:
-
For both Inbound rules and Outbound rules, make sure Source is set to Any for the Allow policy. Leave the Deny policy at their default values:
Important
If your setup requires changing these settings, ensure they do not block Coro's IP address.
-
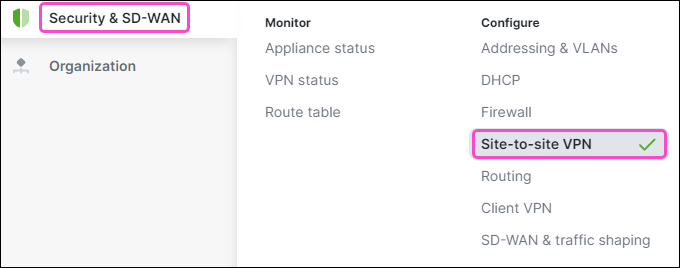
Go to Security & SD-WAN > Site-to-site VPN:
-
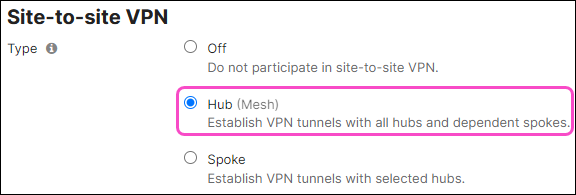
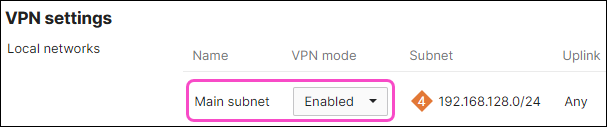
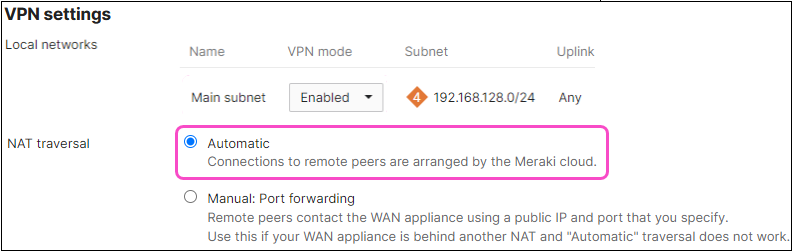
Configure Site-to-site VPN and VPN settings options:
-
Configure Organization-wide settings:
-
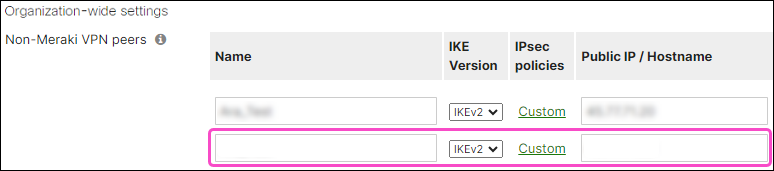
Select Add a peer:
A new row is added to the Non-Meraki VPN peers table:
-
Enter the following settings:
-
Name: Enter a suitable peer connection name.
-
IKE Version: Select "IKEv2".
-
IPSec Policies: Select the Default link.
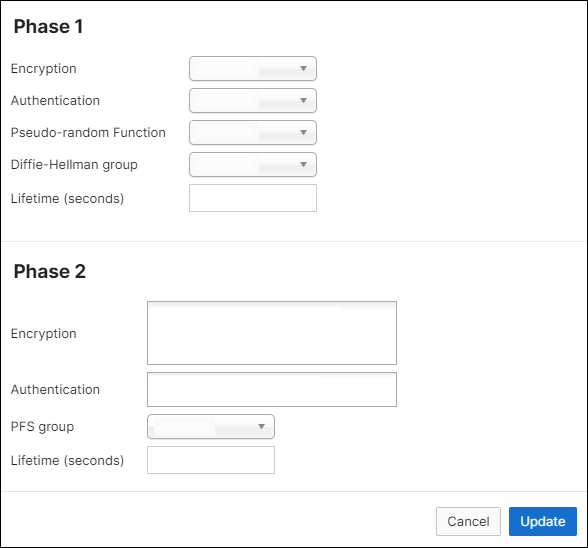
An IPsec policy configuration dialog appears:
-
In the Phase 1 section, make sure your settings match the following:
Field Value Encryption Select "AES-256" Authentication Select "SHA256" Pseudo-random Function Select "SHA256" Diffie-Hellman group Select "14" Lifetime (seconds) Enter "28800" -
In the Phase 2 section, make sure your settings match the following:
Field Value Encryption Select "AES-256" and "AES-128" Authentication Select "SHA256" and "SHA1" PFS group Select "Off" Lifetime (seconds) Enter "28800" -
To save your settings, select Update:
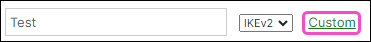
The IPSec Policies link now displays as Custom:
-
-
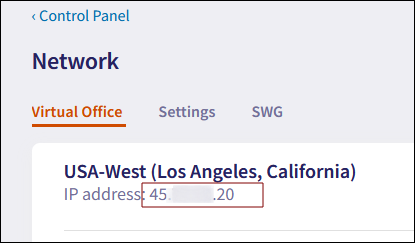
Public IP/Hostname: Enter the Coro public IP address shown in the Coro console.
To retrieve the Coro public IP address:
-
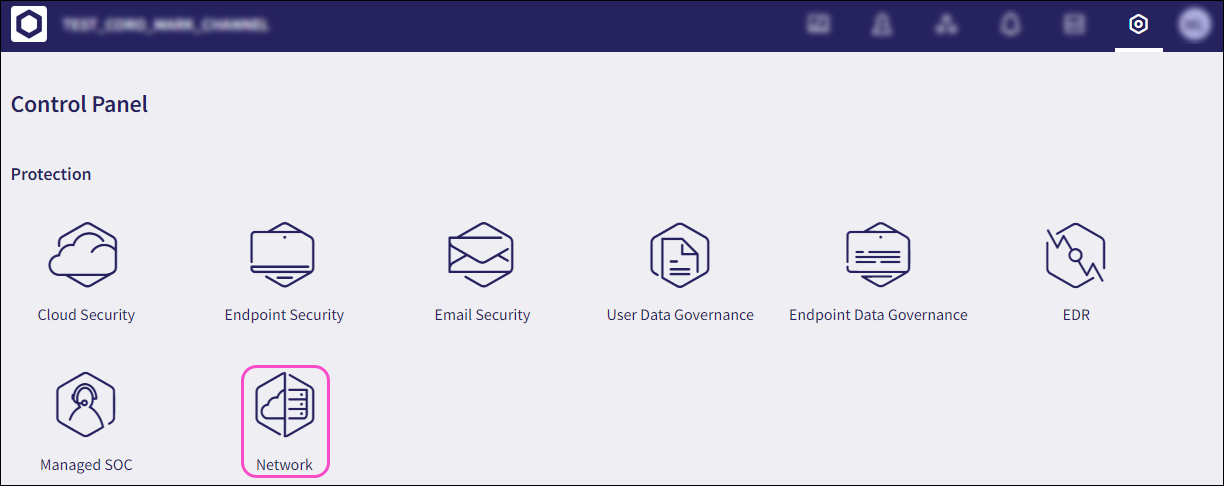
Select Control Panel:
-
Select Network:
The Coro public IP address displays on the Virtual Office page:
-
Local ID: Enter the public IP address of Cisco Meraki's VMX appliance retrieved here.
-
Remote ID: Enter the Coro public IP address retrieved for Public IP/Hostname.
-
Private subnets: Enter "10.8.0.0/16, 10.9.0.0/16".
-
Preshared key: Enter a shared password (secret) or generate a new one.
-
Availability: Select "All networks".
-
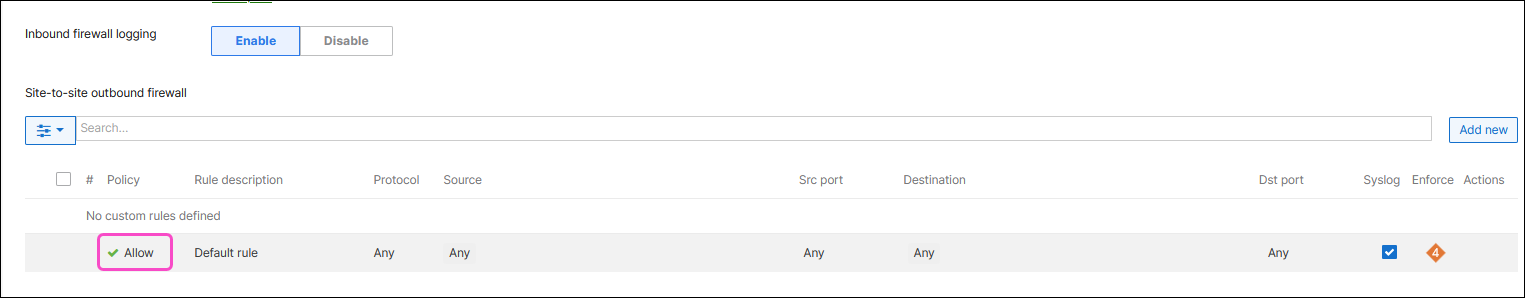
Inbound firewall logging: Select Enable to allow for more granular control over network security and traffic management.
-
Site-to-site outbound firewall: Make sure the policy is set to "Allow":
-
-
-
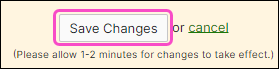
Select Save Changes to save your settings:
Allow one to two minutes for your changes to take effect.
Configuring Coro Network¶
Configure Coro with details of your site-to-site tunnel and firewall:
-
Select Control Panel:
-
Select Network:
-
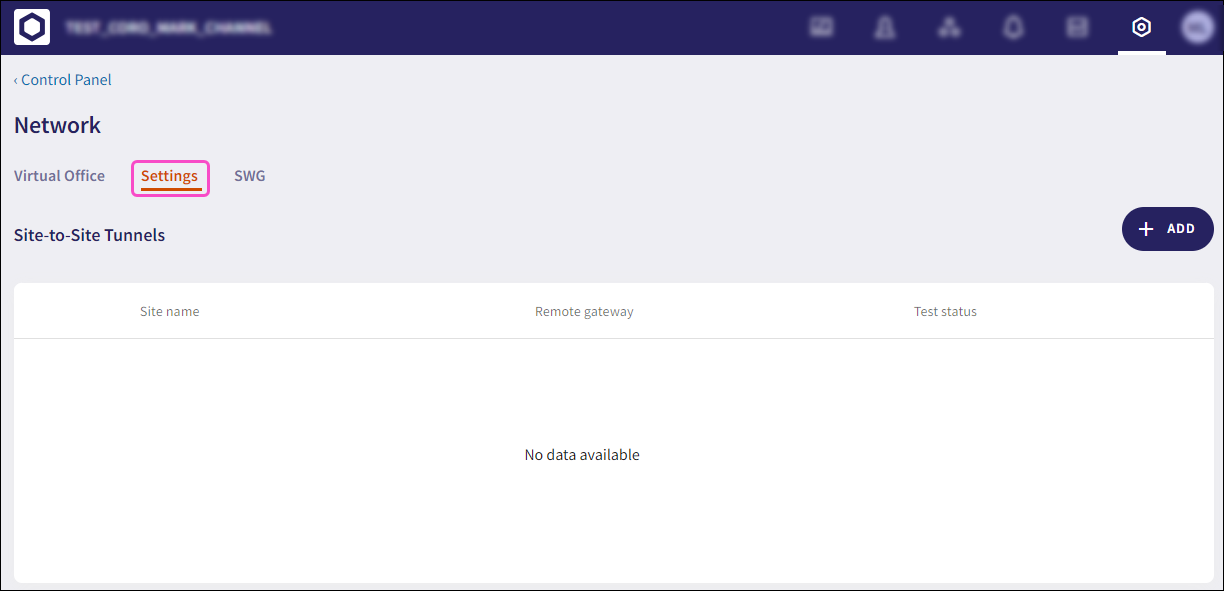
Select the Settings tab:
-
Select + ADD to add a new site-to-site tunnel configuration:
-
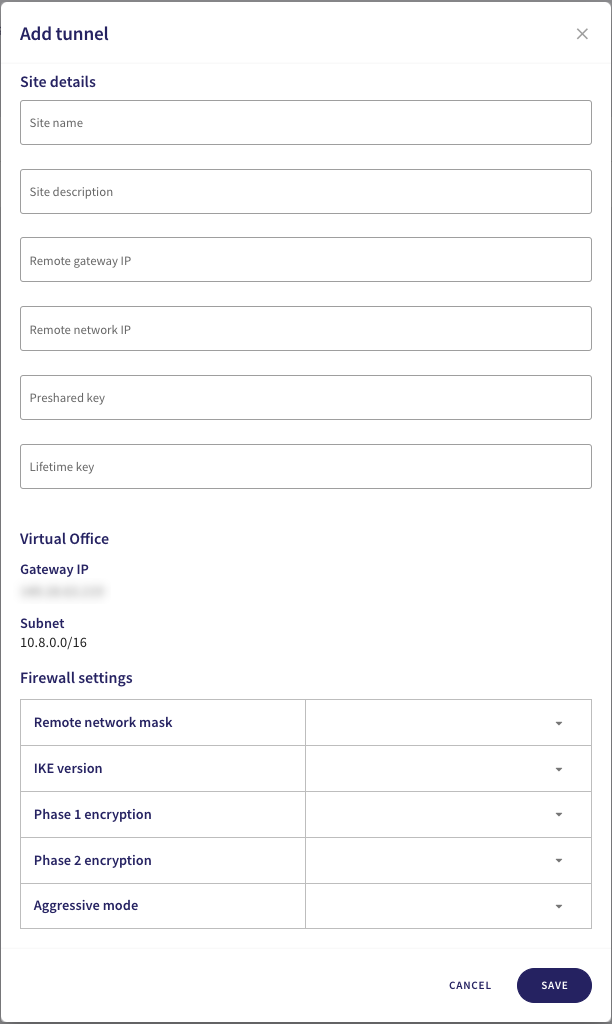
Configure your Site details:
Field Value Site name Enter a suitable name for your site-to-site tunnel
Special characters and spaces are not supportedSite description Enter a suitable short description for the tunnel
Special characters and spaces are not supportedRemote gateway IP Enter Cisco Meraki's public IP address obtained here Remote network IP Enter Cisco Meraki's subnet obtained here Preshared key Enter the preshared key used here Lifetime key Enter "28800" -
In the same dialog, configure the Firewall settings:
Field Value Remote Network Mask Enter Cisco Meraki's subnet obtained here IKE Version Select "IKEv2" Phase 1 Encryption Select "AES256-SHA256-D14" Phase 2 Encryption Select "AES256-SHA256-D14" Aggressive Mode Select "No" -
To save your configuration, select SAVE.